Since Adobe Flash Player is undeniably on its manner out, if you could help me,t, then be aware that several incredible tech websites and online computer evaluate businesses are pronouncing that you will need to begin letting pass of this unique tec,h specifically if you are a content maker or manufacturer. There are many upcoming technologies that are safer and better than the Adobe Flash Player.
One aspect you can’t do away with from Adobe Flash Playe,r though, is that it had a great run. And although this is up for depreciation, it is still capable of managing. It supplies a decent activity with video playback,k, and a perfect variety of websites; nevertheless, game the technology noted. Even if most important browsers have officially moved far from it, the user can favor using Adobe Flash. At the same time, the internet site they’re traveling to is the usage of it.
One aspect you want to look out for,r although when using Adobe Flash Playe,r is that there could be times wherein updates from Adobe itself may additionally have triggered some troubles in its protection or capability that desires to be repatched. If you look at the history of their update,s you may find that a few patches are updated to fix the holes that a previous patch has left open,n especially for Microsoft Windows systems. This is why everybody,y inclusive Adobe,e is slowly finalizing this precise era for desirable.
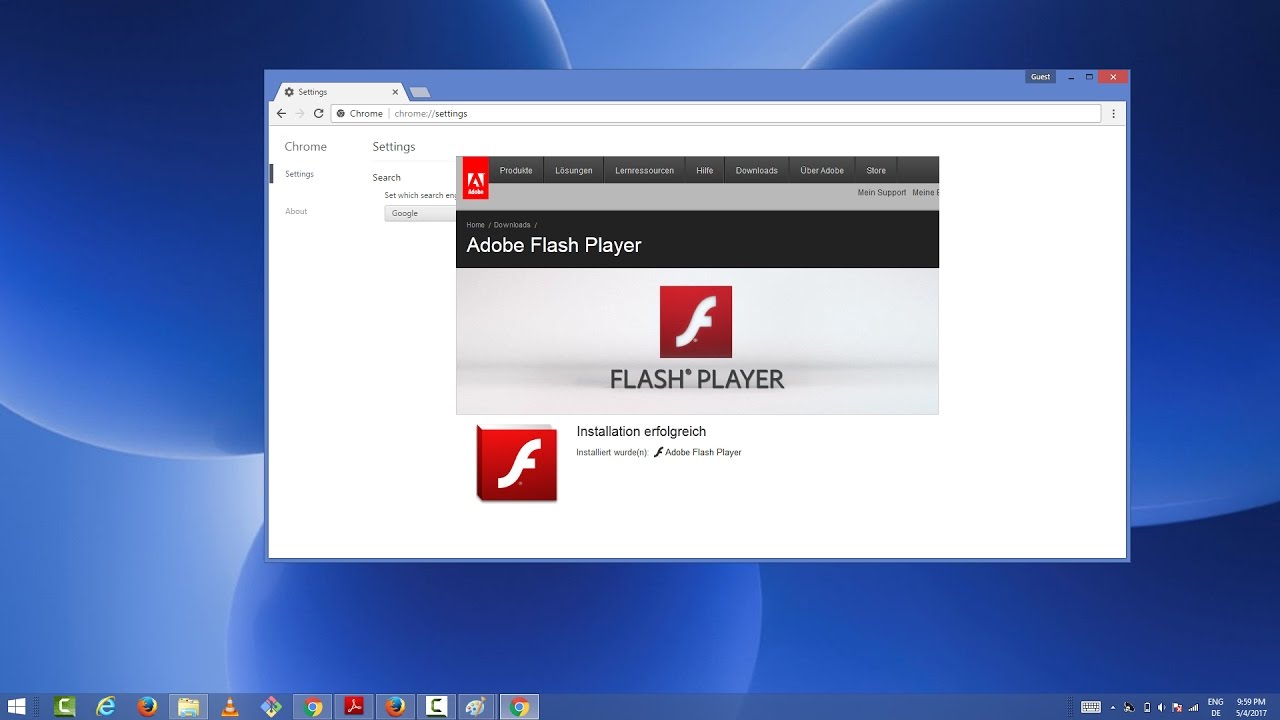
The Adobe Flash Playe,r even though being set aside for higher technology,y nonetheless works for most of the primary platforms, including the trendy generation of the Windows working system s, which is Windows 10. If you continue to fancy using Adobe Flash Playe,r make sure to maintain it updated down to present-day minor update releases to ensure that your structures get the first-class protection they can get.
Recent newsmaker testimonies concerning Microsoft Windows safety highlighted the routine theme that there are “care and feeding” problems related to computers within the dynamic, linked international of the Internet. Just days in the past this month, laptop users of domestic PCs, corporations, and mobile pc customers have been affected. In this case, the problem changed into an animated cursor (commonly, a “.ANI” document)that makes the most, which abused a Windows function and created the issue.
If attacked, the effect potential became high; the latest variations of Windows (2000, XP, 2003, Vista) authorized the computer virus to interaction with “Remote Code Installation and Execution” without the consumer’s understanding. Under the proper situations, sincerely viewing a baited web page ought to set into motion the steps to contaminate the host PC with the gradually damaging malfunctioning software program (malware). The malware should take many forms, in a stealth-like fashion, with customers not able to hit upon something unusual, which makes this specific contamination negative to Internet-coupled PCs. At worst, doubtless,y your PC could robotically join a community of remotely controlled “zombie” computers, equipped to perform extra malicious obligations to the related international below far off course. PCs left powered on for long intervals unattended or in “display screen saver” mode could do masses of downstream damage, switching to a more subdued, “mild-effect” mode when the unsuspecting consumer again to the PC.
This specific exploit was excellent in that a version became reputedly identified and patched in 2005, with a second shape of the take advantage of surfacing in December 2006. Further, the standard practice of using firewalls, anti-adware, and anti-virus applications could no longer avoid infection, leaving many customers with a fake feeling of protection. Reportedly, the make the most ought to occur whether you used Firefox or something aside from Internet Explorer 7 beneath Windows Vista (in protected mode) to browse the internet (although Vista is not immune).
The accurate news- there have been numerous patch updates from Microsoft to correct this condition on the home Windows update website. This real-lifestyles era drama may also light up thoughts about your scenario. Perhaps a terrific time to study my method to ensure a secure and sound computing environment in my organization.? It could be; Array Systems suggests the subsequent primary operational additives be included in a protection overview:
Anti-Virus.
Ensure you have the latest variations and modern definition (signature) updates. Most products have license prices/renewals, which need to be maintained or checked.
Anti-Spyware.
Similar to Anti-Virus in function- ensure updates and variations are contemporary for this tool to be useful. This may be part of a suite of defense merchandise, all with the cause of presenting delivered protection.
Microsoft Update.
An unfastened Microsoft web carrier that provides direct and concise entry to software program updates for Microsoft products (Windows, Office, and many others.) You can set manual or automatic updates. However, you need to understand the ramifications of every method.
Firewall.
Hardware firewall devices are preferred, as a few software-based firewall/Internet security products may be ineffective for positive environments.
Gateway/Content Filter.
Hardware and software program-based devices could provide active safety among inner customers and the Internet and control wi-fi, PDA/cellular users, and far-flung get entry to many others. There (human factors) should be a part of the safety evaluation, which does not involve hardware or software programs. For example, antivirus specialists have referred that possibly 35-40% of virus definitions/signatures are unavailable in the ordinary because of delays in developing remedies or detecting new malware exploits. Therefore, the habits and interaction styles of users turn out to be an important part of a safety protection method, which might consist of the following:
Email.
Don’t open attachments or click hyperlinks unless you know the content. This is similar to internet hyperlinks embedded in e-mail messages and is independent of whether complete-customer packages or net-based browsers are used. Consider while using email or revise business enterprise coverage to standardize its use.
Web surfing.
Stay far away from unknown websites. Currently, Websites are the maximum, not unusual, source of PC contamination. (Even the reliable NFL Super Bowl internet site got infected maximum recently). Spear phishing is specifically harmful. It objectives genuine searching, valid websites, unwritten gramma,r, and customer facts to entice the consumer viewing the website into contamination.

