Attackers have exploited an antique WordPress vulnerability to contaminate more than one thousand websites with malware capable of injecting malvertising and even developing a rogue admin user with complete get entry to privileges, in keeping with researchers. The exploited flaw is mainly located in previous variations of the WordPress tagDiv Newspaper and Newsmag subject matters, in step with a Dec. 14 weblog published via Sucuri safety analyst Douglas Santos. (Sucuri explains the vulnerability in a similar element in an older report.)
“Unfortunately, considering this contamination is associated with a software vulnerability, sturdy passwords, and security plugins will not protect you,” writes Santos, noting that the malicious javascript can be located in a WordPress website’s subject matter options. Following code injection, the malware can execute two viable attack scenarios, relying on the web page visitor: If the traveler is determined to be logged in as an admin user, the malware creates the rogue consumer “simple001” with complete admin privileges, allowing for the complete takeover of the site. If traffic is not logged as an admin and they have no longer been to the website within 10 hours, then the malware commences a series of redirects that send them to various rip-off and commercial websites.
Sucuri first observed this infection fashion earlier this month. Previously, attackers used the equal WordPress flaw to inject a variant of the malicious JavaScript that would display unauthorized pop-user redirect visitors to spammy websites; however, they could not enable an entire website takeover. Sucuri previously pronounced in June that the tagDiv Newspaper subject matter has been brought to more than 40 thousand customers, now not counting pirated copies.
Here is an easy tick list for WordPress owners and publishers. WordPress is one of the maximum famous website systems due to its ease of use. However, it has its problems, and it is because of its popularity, hackers use this platform to try to inject their malware and malicious scripts. WordPress Security has ended up essential today to shield not handiest your website but your emblem popularity.
Unknown Infections
Often WordPress owners are unaware that their internet site has been hacked. Just because your website has been hacked doesn’t always mean you will see an ordinary photo while entering your website. Hackers often hide that they’ve hacked your site by injecting a mailbox and spamming out of your IP deal.
Use our checklist for the principles of valid WordPress Security.
1. Clean and cast off spyware, malware, and viruses out of your PC/Mac before getting into the backend of your WordPress installation
2. Back up your website before you do something easily carried out by using Backup Buddy.
3. Never use ‘admin’ as a username.
4. Always use a sturdy password.
5. Stay Updated – Ensure your WordPress Installation and WordPress Plugins are usually up to date. See the Latest WP Security Updates in the sources section beneath.
6. Limit Login Attempts – Ensure you reduce the login attempts to around three. Could you not make it easy for the hackers?
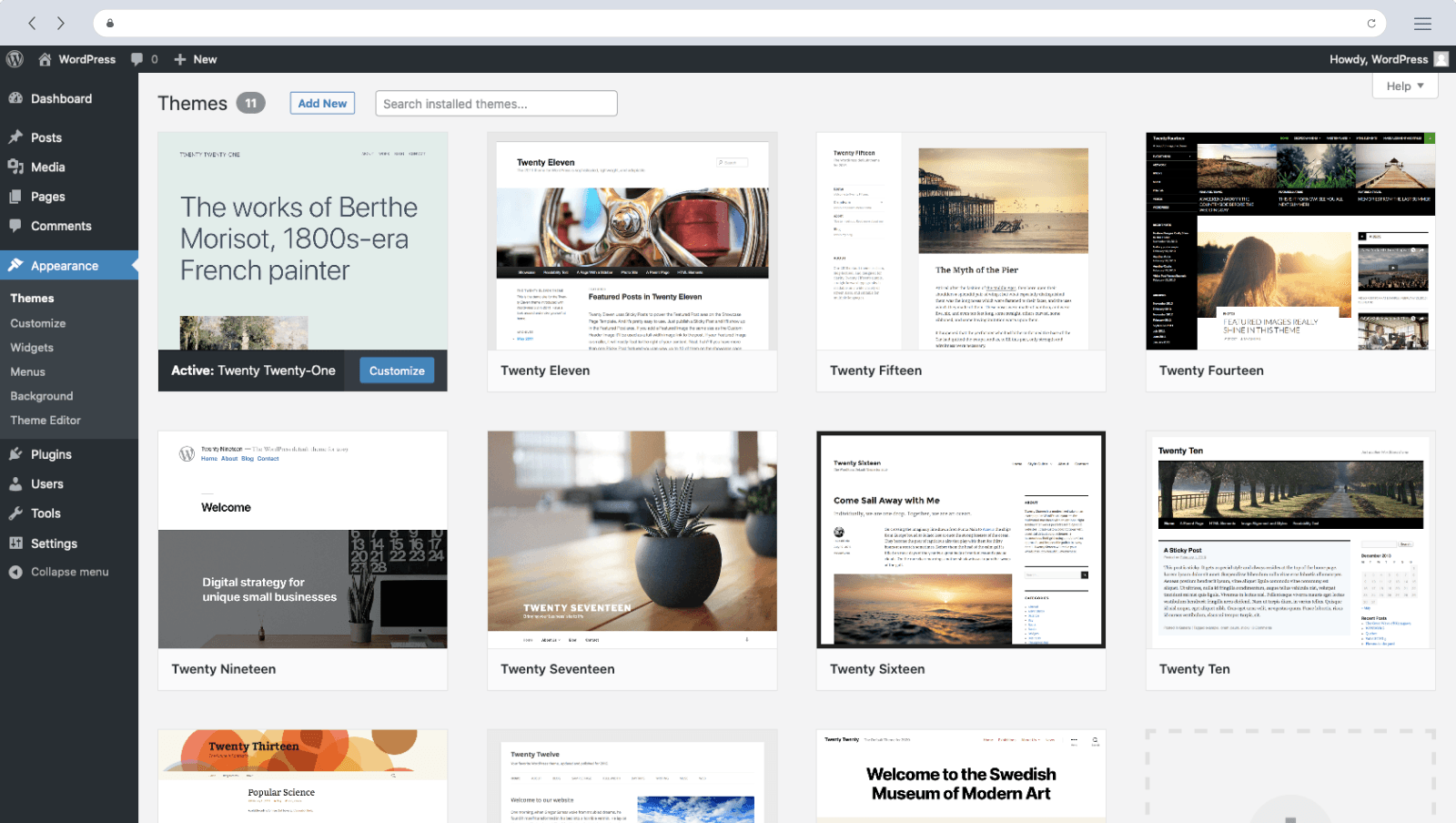
7. Remove unwanted WordPress Themes – When subject matters are on your website, and they exit of date, Hackers use those to gain entry. Only have the subject you’re using mounted and hold that updated.
8. Spring Clean – Your WordPress website might also have other folders based on your server. Do you need them, or are they improvement areas? If you do not need the folders, delete them.
9. Your Hosting Company – Make positive you use a website hosting employer specializing in WordPress installations. WordPress servers want unique attention to defend your internet site.
10. Double Layer Authentication – Use a brought layer of safety.
Summary
While the checklist above is not an exhaustive list, it’s miles a necessary stage of security. Protection is the beginning of the manner; monitoring your internet site daily is critical. We comprehend that many website owners don’t have the time or the know-how, so we provide three services observed in the assets section underneath. Has your web website ever come beneath assault? Have you experienced an SQL injection assault? Would you understand the symptoms of this kind of protection chance if you did? Do you know how desirable your net applications’ safety and general internet site safety is? Are you vulnerable to security threats?
Every day tens of millions of network servers and structures are probed, scanned, and attacked. Attacks have long gone beyond viruses and worms. It is primarily liable to attack net programs, utility security software programs, net server safety, and standard internet site safety. One of the more significant malicious hacking methods is SQL injection, also called an inference attack. In an inference or SQL injection attack, the attacker adds SQL code to an internet-shaped input container to get admission to assets or trade the facts.
Suppose you’ve got a shape on your web page that requests a username and password for admission into a relied-on database. If a consumer enters the ideal response, the system authenticates the person and permits access to the guarded pages. If the user enters the incorrect username and password, they’re commonly sent a few blunders message types and request the facts again. At some factor, if the appropriate data isn’t supplied, the system times out, and the user has to begin all another time.
Sometimes excessive numbers of errors invoke a blocklist of the username and password ensuing inside the attempted to get the right of entry to being denied. What might occur if an attacker entered an SQL command rather than a username and password? The order can be executed in approximately 60 in line with a cent of the web programs using dynamic content material, permitting the attacker to download the entire database or worse.
According to many professionals, SQL injection assaults are possible because internet software code isn’t secured throughout software development. One of the first-class ways to ease programs is by restricting access to authorized access to the application using Secure Shell or Secure Socket Shell (SSH). SSH presents robust and at-ease communique over unsecured channels. SSH uses a TCP connection and encrypts the consultation utilizing public-key cryptography and the symmetric encryption algorithm to defend the talk.

